The IAS Risk Labs has called the attack a Calidoscope because it is always changing to avoid detection. According to statistics, two and a half million new devices are compromised every month, 20 % of them are found in India. In other areas where the Cleudoscope has been detected, they include Indonesia, the Philippines and Brazil. Pushing this risk extension is the installation of malicious apps through the third party’s App Store fronts.
Examples of intervention ads that appear on Android phones that have installed malicious apps. | Image credit
Caleedoscope works like this. A Android user installs an app from the Play Store that looks and even runs like a legitimate app. The third party app store has a malicious copy of the app. Messages and social media instruct users to install malicious versions of these apps through third party app stores and directly install. The owner of the Android device believes it has installed a legitimate app, and the advertisers believe their ads are being viewed on legal apps.
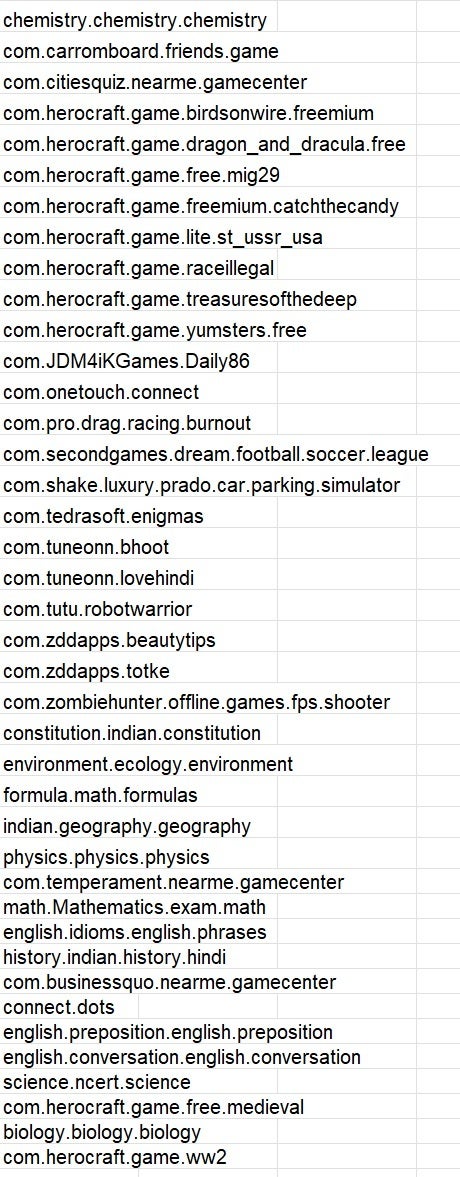
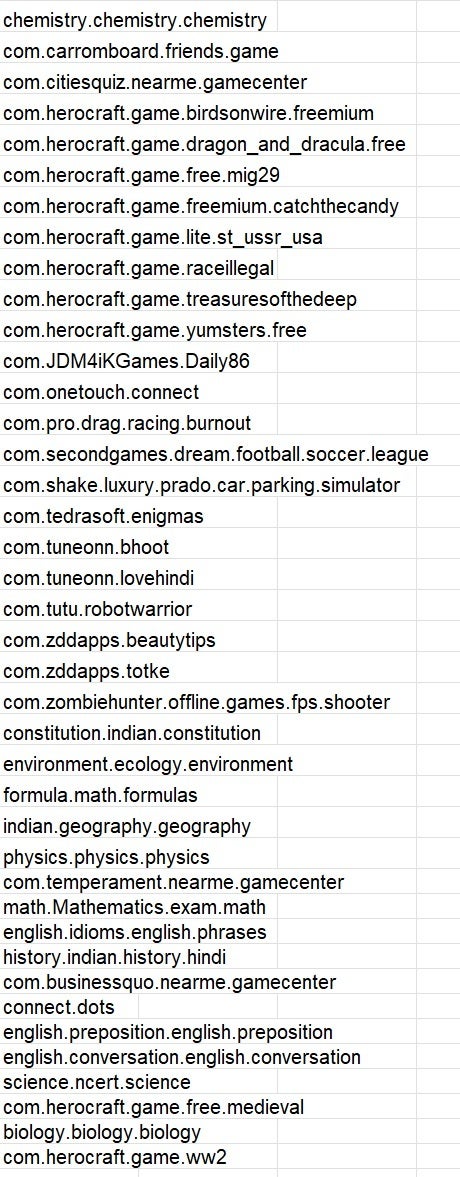
If you have any of these apps on your Android phone, delete them immediately. | Image credit
Instead, once a malicious version of the app is installed on a phone, it shows ads of interference, including photos and videos of full screen that do not require any interaction with the user to operate. You can see how distressing this unfortunate device owners who can end up with a phone that is making a large sum of money for cyber criminals and prevents users from watching their display.
An incredible two -and -a -half million new installs of Cledoscope -affected apps make it a very serious and dangerous situation for Android users every month.


